How to Protect Government Websites from Critical Security Threats
Introduction
Government websites are prime targets for cyberattacks due to the sensitive data they hold and their role in national security. A successful attack can lead to data breaches, service disruptions, and even national security risks. Protecting these websites from critical vulnerabilities requires a proactive cybersecurity strategy. In this blog, we’ll explore the best practices and security measures to safeguard government websites from cyber threats.
1. Conduct Regular Security Assessments
Penetration Testing
Performing regular penetration tests helps identify vulnerabilities before attackers can exploit them. Ethical hackers simulate real-world attack scenarios to uncover security weaknesses.
- Tools: Burp Suite, Metasploit, Nmap, OWASP ZAP
- Frequency: At least once every quarter
- Action: Patch vulnerabilities based on test results
Vulnerability Scanning
Automated vulnerability scanning helps detect misconfigurations and outdated software.
- Tools: Nessus, OpenVAS, Qualys
- Action: Run scans frequently and fix identified vulnerabilities
Bug Bounty Programs
Encouraging ethical hackers to report vulnerabilities through a responsible disclosure policy (RDP) can significantly enhance security.
- Platform: HackerOne, Bugcrowd, Synack
- Action: Set up a bug bounty program with clear rules
2. Implement Strong Access Controls
Multi-Factor Authentication (MFA)
Implementing MFA ensures that even if an attacker steals credentials, they won’t be able to access the system.
- Action: Enable MFA for all admin and privileged accounts
- Tool: Google Authenticator, Microsoft Authenticator, Duo Security
Least Privilege Principle
Users should have the minimum level of access required to perform their tasks.
- Action: Restrict admin access to only necessary personnel
- Tool: Role-based access control (RBAC) implementation
Session Management
Implementing proper session controls prevents unauthorized access due to idle sessions.
- Action: Set session timeouts and enforce automatic logouts
- Tool: JWT, OAuth, Secure Cookies
3. Secure the Web Application
Web Application Firewall (WAF)
A WAF filters and monitors HTTP traffic to prevent common attacks.
- Tools: Cloudflare, ModSecurity, AWS WAF
- Action: Deploy a WAF to block malicious requests
Input Validation
Proper input validation prevents SQL Injection, XSS, and CSRF attacks.
- Action: Use parameterized queries and sanitize input fields
- Tool: OWASP ESAPI, Web Application Frameworks (Django, Laravel, etc.)
Content Security Policy (CSP)
A CSP header prevents unauthorized scripts from executing in a browser.
- Action: Set up a strong CSP to block malicious scripts
- Example:
Content-Security-Policy: default-src 'self'
4. Monitor and Respond to Threats
Security Information and Event Management (SIEM)
A SIEM system collects and analyzes logs in real-time to detect cyber threats.
- Tools: Splunk, Wazuh, ELK Stack
- Action: Monitor logs for suspicious activity and respond immediately
Log Analysis
Regular log analysis helps detect anomalies and potential attacks.
- Action: Store and analyze logs for unauthorized access attempts
- Tool: Graylog, LogRhythm, Security Onion
Incident Response Plan
Having an incident response (IR) plan in place ensures quick action during a security breach.
- Action: Develop and regularly update an IR plan
- Steps: Detection → Containment → Eradication → Recovery
5. Keep Software and Systems Updated
- Regular Patching: Apply software updates and security patches immediately.
- Automated Updates: Enable automatic updates for security-critical components.
- Remove Unused Software: Unused applications can be entry points for attacks.
My Experience Reporting a Critical SQL Injection Vulnerability
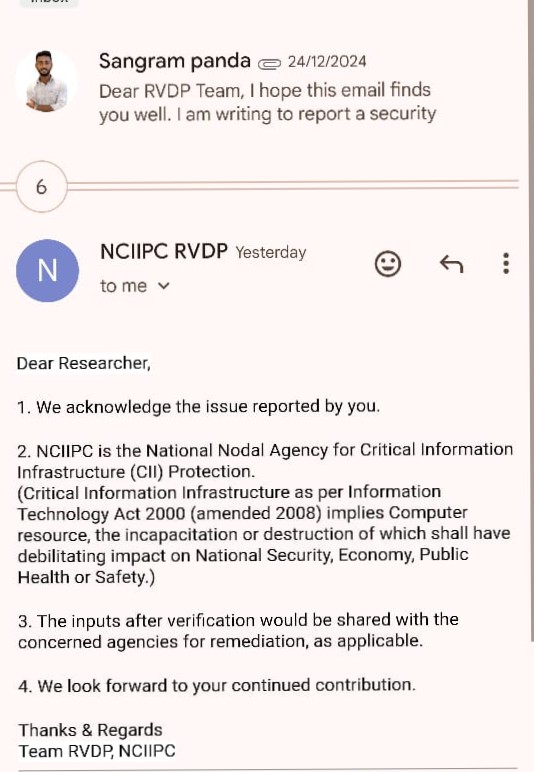
As a cybersecurity researcher, I recently discovered a critical SQL Injection (SQLi) vulnerability in a government website. Understanding the potential risks, I immediately followed responsible disclosure practices and reported it to the National Critical Information Infrastructure Protection Centre (NCIIPC).
NCIIPC, as the National Nodal Agency for Critical Information Infrastructure (CII) Protection, plays a vital role in securing systems that, if compromised, could impact national security, the economy, public health, or safety. After my report, I received an appreciation email acknowledging my efforts in securing government infrastructure. This experience reaffirmed the importance of ethical hacking and responsible disclosure in strengthening cybersecurity.
Conclusion
Securing government websites requires a multi-layered security approach involving regular assessments, strong access controls, application security, and continuous monitoring. By following these best practices, governments can mitigate cyber threats, protect sensitive data, and ensure website availability.
Advanced Cybersecurity Training
🔹 Need advanced cybersecurity training? Join our cybersecurity courses at Cybknow and learn how to secure critical infrastructure!